
New scam targeting financial and recruitment companies
Summary:
Recently several clients have discovered they are victims of CPL Malware – a new scam targeting recruitment and financial companies. These were not random attacks. Each company was carefully targeted, and the attacks were activated by a single click!
Please, use the below information to educate and remind your team how to block attacks. Stop this from happening to you!
CPL Malware is a targeted attack where scammers send fake resumes to recruitment companies or fake invoices / receipts to finance companies. If clicked, the attached documents have the potential to infiltrate your entire system. Usually, scammers will try to access your bank accounts or steal data to hold it to ransom for large sums of cryptocurrency.
How:
1. Scammer seeks out advertised positions and emails a generic email to the Recruitment Company or HR manager with a malicious link. Such as below:
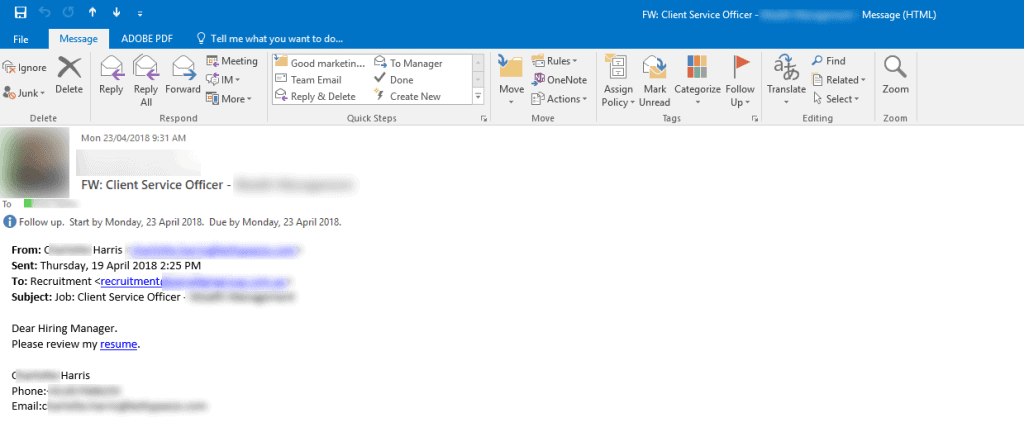
If you are a Finance company, scammers will send a similar email but with a link to an invoice or receipt.
2. Clicking the ‘resume’ or ‘invoice’ link automatically downloads a compressed .CPL file onto the victim’s computer.
3. Finally, the embedded malware will monitor victims’ access to bank sites, redirects victims to malicious sites, or hijacks victims’ banking sessions and/or data.
This is how easy it is for a scammer to trick your employees:
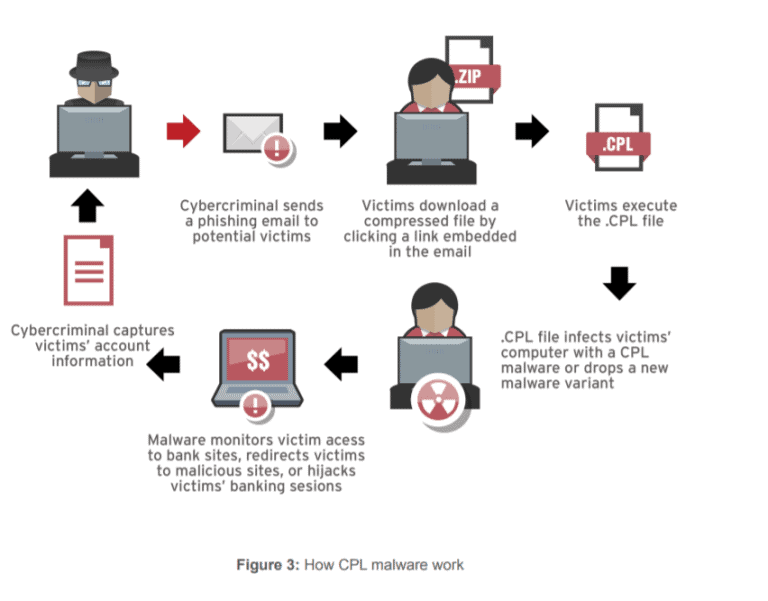
Source: (Mercês)
How does CPL bypass your anti-spam mail filtering solution?
Scammers take care to appear legitimate. Generally, CPL emails will pass through a filter because they contain no obvious suspicious content, only vague one-line sentences with a link.
What can you do?
The method of attack does not change – just WHO gets targeted! Keep reminding your team to be alert! Please share this article with them so they know what to look at for, and strengthen your firm’s defenses. Attacks are now so common, we strongly recommend you remind your team on a regular basis to be careful with emails.
1. Check links and attachments
- Ensure attachments are Word Documents or PDF’s, and NOT links or Zip Files.
- Do not trust any links or suspicious attachments such as Zip Files or PowerPoint documents.
- If you are suspicious of a link, hover over the link and check it is not directing you to a suspicious website / location.
- Educate your team to be cautious about opening attachments and clicking on links.
2. Firewalls give added defense
- Even if someone in your organisation clicks a malicious link, a Firewall will prevent viruses / Trojans from entering your network.
- Have a firewall that supports deep level content inspection to prevent viruses entering your network. IMP: Just having a firewall is not enough – it needs to be correctly configured to protect against threats. A correctly configured firewall is a also vital step in preventing Trojans from penetrating your network.
3. Unsure? Call itro to check legitimacy
- If you are unsure about an email, don’t click anything, call itro 1300 10 3000
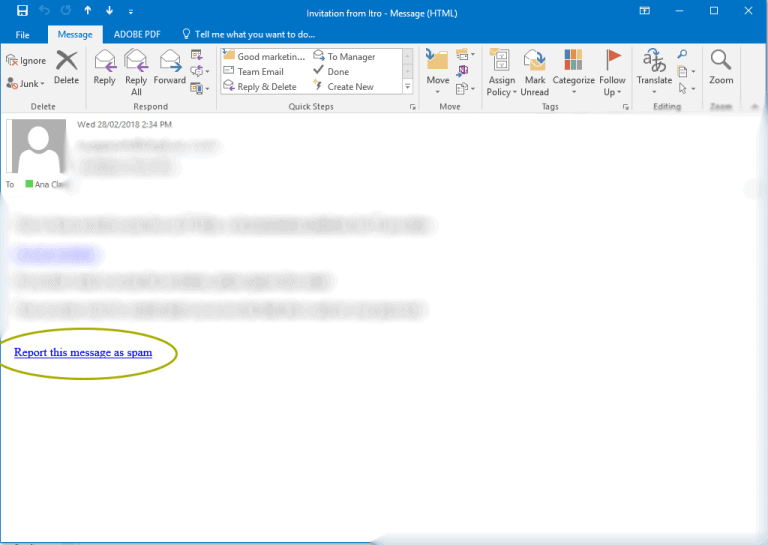
4. Report the message as spam
- Furthermore, if you are using itro Mail Scan, report the message as spam (see below):
Related Articles
- 5 steps to protect your data
- Display name spoofing
- 9 out of 10 cyber-attacks are delivered by email
- The latest scams circulating this week
Tips on how to spot an email as illegitimate:
- Non-personalisation or incorrect personal details
- Incorrect or non-personalised greetings, for example “Hi Manager”
- Suspicious or hidden email address, therefore, always check domain addresses because Netflix will only ever send an email from a domain of @Netflix.com
- Misleading hyperlinks. Before clicking any links, hover over it and check the domain it is linking you to and if they look suspicious do not click them and instead refer to the companies website
- Incorrect domain name, for example legitimate emails from Bingle have the domain @bingle.com.au
- Outdated logos or incorrect brand imaging

