Security Alert: Petya Ransomware Attacks
“Petya” Ransomware Attacks
Last month it was WannaCrypt that caused havoc worldwide. Yesterday another ransomware attack –malicious software dubbed “Petya” – is affecting computers rapidly across Europe and Ukraine. A post in Hacker News reports Petya is spreading virulently affecting banks, telecom, businesses and power using the same Windows SMBv1 vulnerability that the WannaCry ransomware used to infect over 300,000 computers.
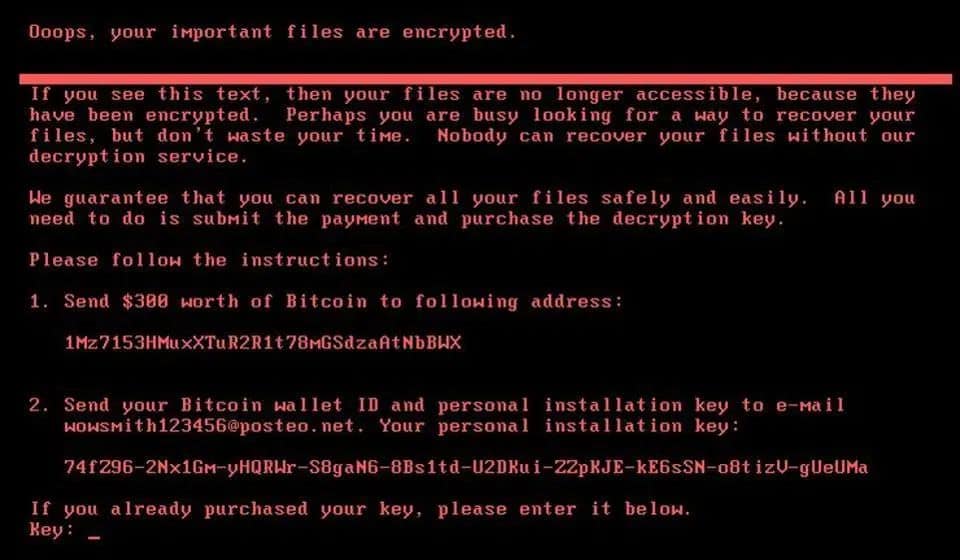
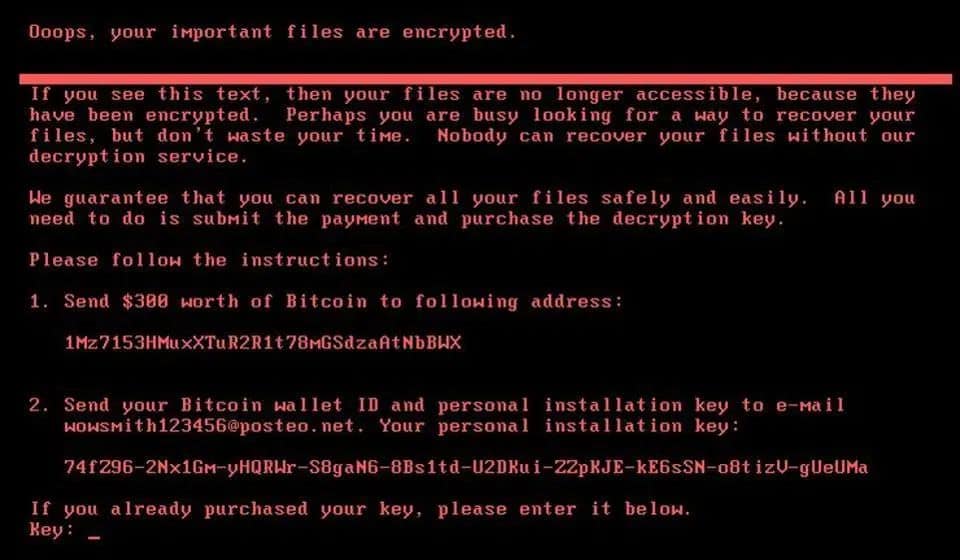
A screenshot from the new ransomware attack (Source: Symantec)
Similar to WannaCrypt, Petya is a worm. It initially infects a computer through an email attachment and then spreads itself – without further user interaction – to other computers on the local network.
Data released by Kaspersky Lab, suggests 98 percent of computers affected by WannaCrypt (which used the same vulnerability) ran Windows 7. While Microsoft patched the vulnerability in Windows 7 & 8.1 in April, it highlights that earlier versions of Windows are inherently less secure that Windows 10.
While it’s impossible to immunise a computer network from attack, itro strongly recommends implementing a multilayered defence to reduce the likelihood of such attacks succeeding, or limiting potential damage if an infection occurs. A good defence plan should include using an up to date operating system (limiting the attack surface), implementing strong mail mailing (to catch incoming attacks), and robust endpoint monitoring (to proactively identify successful infections).
itro recommends that you upgrade your computers to Windows 10, as there are numerous security improvements to the operating system that are not available in earlier versions of Windows.
Interested in finding out about CryptoLockers and how to protect yourself?

