Watch out for the latest email scams
Fake emails circulating impersonating St George Bank and QuickBooks
Scammers target brands, such as the above, are they are reputable and have a large customer base. It’s likely most readers are using or have used in the past one of the above services.
Are you using a Mail Filtering Solution? Such as itro Mail Scan
- Yes – great, any emails with the potential to harm your business are blocked from reaching inboxes
- No – you are not protected, malicious emails are entering your inbox. Staff may unknowingly click a malicious link allowing a cyber criminal access to your network. Once cyber criminals have access to your network they will generally hold your data at ransom demanding large amounts of money
- Unsure – if you receive constant spam or unwarranted emails, it’s likely you do not have a Mail Filter solution
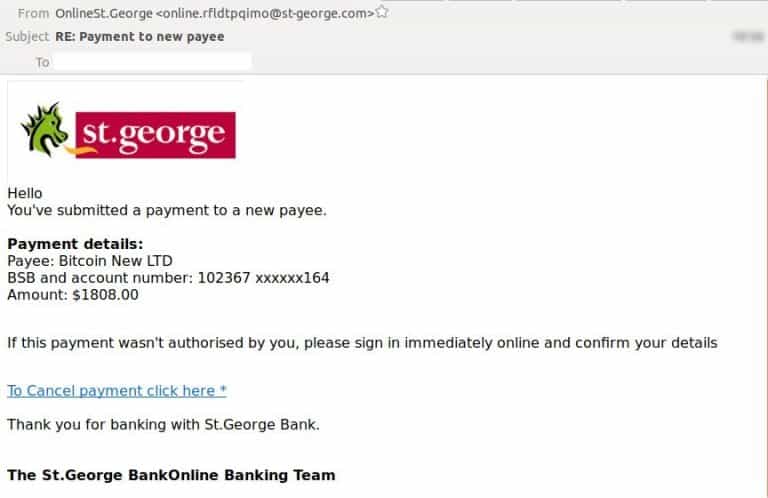
1. Fake St George Bank
Below is a phony email claiming to be from St. George, asking you to ‘immediately’ sign in. However, if you click the link it re-directs you to a phony page asking for login details. Once you enter your credentials, the scammers now have your details.
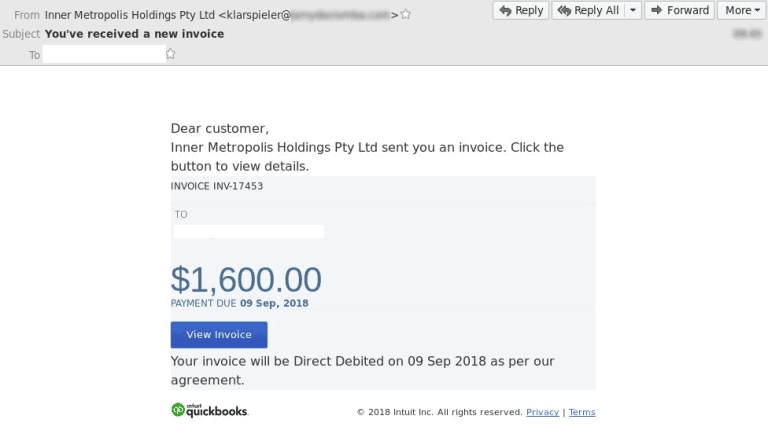
2. QuickBooks – Fake Invoice
An email claiming to be form QuickBooks continues to circulate claiming with a phony invoice of $1,600. Clicking the link directs the receiver to a malicious website. Tips to spot this email as illegitimate: wrong display name, incorrect branding and it’s not addressing you.
Tips on how to spot an email as illegitimate:
- Non-personalisation or incorrect personal details
- Suspicious or hidden email address, therefore, always check domain addresses because Netflix will only ever send an email from a domain of @Netflix.com
- Misleading hyperlinks. Before clicking any links, hover over it and check the domain it is linking you to and if they look suspicious do not click them and instead refer to the companies website
- Incorrect domain name, legitimate emails from Bingle have the domain @bingle.com.au
- Outdated logos and incorrect brand imaging